BTC Tumbles Back to $64,000 as IBM Becomes Latest AI Target for Enthusiasts and Professionals
A sudden crypto wobble met a spike of attention on enterprise models, and the collision matters for every team buying compute, building copilots, or hiring AI security.
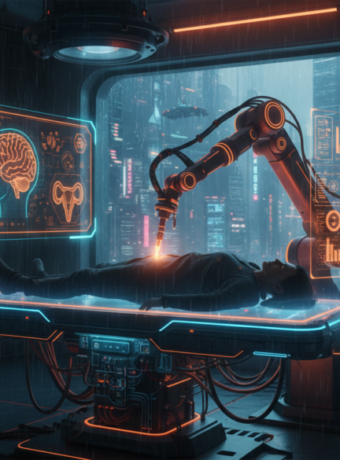
The floor of a downtown trading desk looked like a barometer for the broader tech economy: traders refreshing price feeds, PMs whispering about capital expenditure, and an engineer in the corner running a security scan against a corporate AI endpoint because curiosity beats sleep. That human itch to poke systems is now part of the market story, not a sidebar.
On the surface the obvious read is simple: risk off, traders sell, bitcoin falls. The deeper, underreported angle is that the same forces that push traders to flee also shift where companies spend on AI, and that reallocation hands both opportunity and headache to security teams, open model communities, and infrastructure vendors.
Why Wall Street Blamed AI Spending First
Markets linked the price drop to a broader pullback in risk appetite triggered by concerns about heavy AI-sector capital spending and softer macro data. That connection surfaced in coverage explaining how investor nerves around AI capex contributed to a rapid unwind in risk assets. (economictimes.indiatimes.com)
Technology investors recalibrating AI returns makes sense in a world where GPU minutes and data center slots are visible line items on a CFOs spreadsheet. When long duration bets suddenly feel less certain, nonyielding assets like bitcoin get repriced faster than a corporate deck can be updated.
The day Bitcoin slid under $64,000
The crash itself was abrupt and severe, with Bitcoin briefly breaching $64,000 and liquidations in the billions that amplified moves across crypto equities and derivatives. Traders and analysts called it a capitulation phase that rapidly erased leveraged positions and tested technical supports used by institutional desks. (roic.ai)
That sort of violent repricing forces companies to rethink the tempo of AI rollouts. Planned clusters of GPUs get delayed or scaled back, and procurement teams start questioning contract lengths that were signed during a different mood. Nobody ever yelled at a vendor for buying too few GPUs, except in management postmortems.
IBM suddenly in the crosshairs of curious engineers
Parallel to the market rout, a flood of hobbyists, security researchers, and professional red teams have been training their tools on enterprise-grade models and platforms. Open source scanners and red team frameworks now list IBM endpoints among their supported backends, making watsonx and Granite models regular targets for automated probes. That pattern converts theoretical risk into measurable attack surface. (appsecsanta.com)
The attention is not inherently hostile. Many scans are defensive research or compatibility testing. That said, public tooling lowers the barrier for both benevolent stress tests and opportunistic probing. It is a bit like publishing your car manual and then being surprised when a fan community tunes the engine at three in the morning.
Granite’s openness changes the playbook
IBM’s Granite family of models has been iteratively opened and distributed across partner platforms in a manner designed to accelerate enterprise adoption and transparency. The company published details about Granite 4.0 that emphasize efficiency, signatures for provenance, and distribution via major ecosystems. That openness accelerates both adoption and scrutiny from the community. (ibm.com)
For enterprises, more transparency means easier audits and faster integration. For attackers and auditors alike, it means known checkpoints to test against and clearly defined interfaces to interrogate. In short, openness is a productivity multiplier that works for both defenders and testers.
The industry just learned that being the most transparent player does not remove the need for hardened defenses.
The cost nobody is calculating
If bitcoin falls and tech valuations wobble, capital for sprawling AI infrastructures tightens. The immediate math is straightforward: every 10 percent tightening of projected AI budgets reduces contracted GPU hours by thousands to tens of thousands per quarter for mid sized deployments. That reduction cascades into smaller model deployments, more emphasis on efficient inference, and a rapid pivot to using smaller, optimized models in production.
A practical scenario: a retailer planning a fleet of 200 inference instances at 80 dollars per GPU hour for peak traffic might see an annual bill drop by several million dollars when they choose optimized Granite variants or aggressive quantization. That is real money and it changes vendor conversations overnight. Also it explains why a product manager might suddenly love a 3 billion parameter model that runs on cheaper hardware; thrift is sexy when budgets tighten, and no one said thrift had to be boring.
The security tooling boom and who profits
The rise of accessible red team tools plus enterprise risk committees demanding robust guardrails is creating a small but lucrative market for AI security platforms, consulting and managed red teaming. Vendors and independent researchers who can demonstrate prompt injection resilience, data leakage tests, and provenance checks will find buyers among risk averse CIOs.
Short sellers will probably wish this sector did not exist, but defenders will happily pay for CVE grade audits of LLM pipelines. One could argue that auditing LLMs is the cybersecurity profession’s new revenue diversification, which feels like a responsible midlife crisis.
Risks and open questions that stress-test claims
Counting on openness to guarantee safety is naive; attack surfaces grow with accessibility. Automated scanners can inadvertently find sensitive behaviors or create liability by logging or exposing PII during tests. Regulators asking for documented governance, and buyers asking for provable provenance may clash when red teams publish findings that implicate customers.
Another open question is whether reduced AI capex will slow progress enough to reshape model economics, or simply redirect spending to software for governance and efficiency. The answer matters for infrastructure providers and for companies that monetize model serving and observability.
Practical next steps for businesses
Security first: treat model endpoints as production services and run continuous red team tests that include prompt injection, data exfiltration probes, and provenance checks. Procurement second: renegotiate capacity with spotty commitments and favor models that are cost efficient at inference time.
Vendor selection should prioritize signed checkpoints and verifiable supply chains while running small pilots to validate throughput and safety. Do not deploy enterprise copilots without a documented playbook that ties model outputs to audit logs and business ownership.
A short forward-looking close
Market gyrations that push bitcoin to the low sixties are noise if not paired with a strategic reset; the real story is how capital reallocation forces the AI ecosystem to prioritize efficient models, hardened deployments, and governance tools that scale beyond pilot projects.
Key Takeaways
- The bitcoin slide to about sixty four thousand dollars amplified scrutiny on AI spending and forced companies to reassess deployment pace. (fxleaders.com)
- IBM’s Granite family is both a target and a tool for the community, thanks to open distribution and model signing. (ibm.com)
- Public red team tooling now supports IBM endpoints, turning curiosity into measurable security demand. (appsecsanta.com)
- Businesses should shift spend toward efficient inference and invest in continuous LLM security testing to protect production data and liability.
Frequently Asked Questions
Why did bitcoin fall and should AI teams care about crypto price swings?
Because a sudden reappraisal of AI sector capital spending can tighten risk appetite across markets, budget committees react, and procurement cycles slow. AI teams should care because budget reallocation changes what and how much gets deployed.
Are IBM’s Granite models safe to use in production today?
Granite emphasizes transparency and provenance, which reduces some deployment risks, but safety depends on integration choices, guardrails, and continuous testing. Treat model safety as an ongoing engineering and governance responsibility.
What immediate steps should CIOs take after a market-driven budget squeeze?
Prioritize high ROI projects, move noncritical workloads to optimized models, and require vendor SLAs that include security testing and signed model artifacts. That reduces both cost and exposure.
Can community scanners hurt enterprises by probing production endpoints?
Yes, unsupervised probing can expose data or create logs that include sensitive information; coordinate with providers and adopt staged testing environments to reduce accidental leaks. Responsible disclosure policies matter more than ever.
Will this trend slow enterprise AI adoption?
It will change adoption patterns by favoring efficiency and governance. Enterprises that adopt these disciplines will continue, while those that ignore them will find pilots stalled by audits and board questions.
Related Coverage
Readers who want deeper background should explore how model provenance and cryptographic signing work, the economics of GPU spot markets, and case studies of successful LLM governance frameworks. Coverage on managed red teaming and vendor comparisons for inference efficiency will also help procurement teams make faster, safer decisions.
SOURCES: https://www.roic.ai/news/bitcoin-plunges-to-15-month-low-briefly-breaks-below-64000-amid-broader-market-pressures-02-05-2026, https://economictimes.indiatimes.com/markets/cryptocurrency/bitcoin-rebounds-near-64000-after-intraday-slide-to-60000-amid-macro-and-ai-sector-worries/articleshow/127971834.cms, https://www.fxleaders.com/news/2026/02/06/bitcoin-crashes-to-64000-11-5-daily-plunge-tests-former-cycle-highs-as-bearish-momentum-accelerates/, https://www.ibm.com/new/announcements/ibm-granite-4-0-hyper-efficient-high-performance-hybrid-models, https://appsecsanta.com/garak